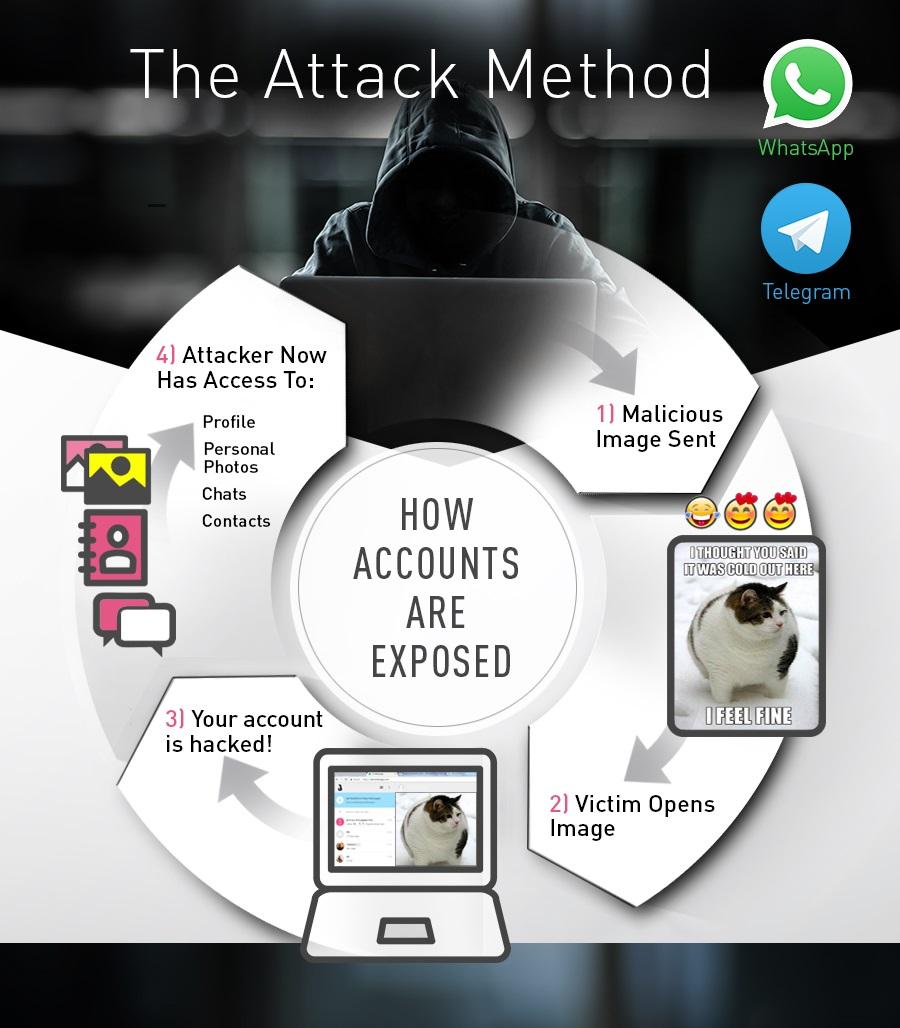
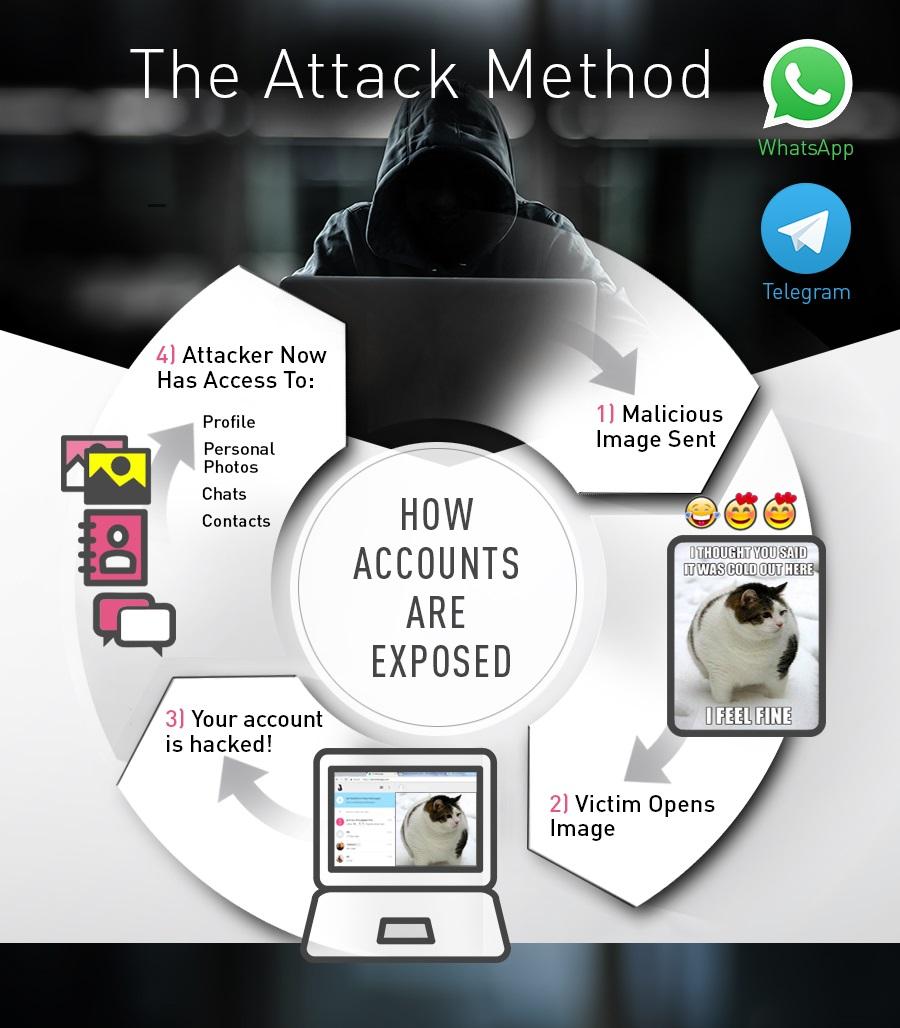
The security firm Checkpoint revealed on Thursday that it had found a serious vulnerability on the WhatsApp Web client that could allow an attacker to gain full access to contacts, chats, and shared docs using a malicious code hidden in what seemed to be an innocent photo sent over chat. This problem was exclusive to the web version, which requires a QR code sent from the smartphone app to run on any browser.
The security breach was made by sending a URL through a call to a FileReader object from the HTML5 API used by the client. This problem may have affected thousands of users who found themselves infected just by downloading and clicking on the sent image. Checkpoint also revealed that Telegram had been affected by a very similar procedure, but this was quickly rebutted as in the case of Telegram besides having to download the infected file you had to try to play it in a new tab, meaning the conditions were anomalous and quite improbable.
Both the Telegram and WhatsApp web clients have solved the problem, and in the latter case the company spokesperson contacted several media outlets to notify users of the correction and highlight how quickly the breach had been closed. Users should simply restart their browsers for the changes to take effect.
In this case, the problem affected the web client only, but it’s not the first time that WhatsApp’s security has raised eyebrows for its patchy protocols (it was just a month ago that they finally rolled out two-step verification) and the number of scams floating around on the app. The solution? To be super cautious and keep the app totally up to date.