Given that antivirus tools on Android are of questionable utility, the best way to protect yourself when it comes to using potentially malicious apps is to turn to an infallible detection system: mass analysis by users of the apps themselves. Koodous is a platform to analyze and rate apps that can search your device to check if you have something undesirable installed.
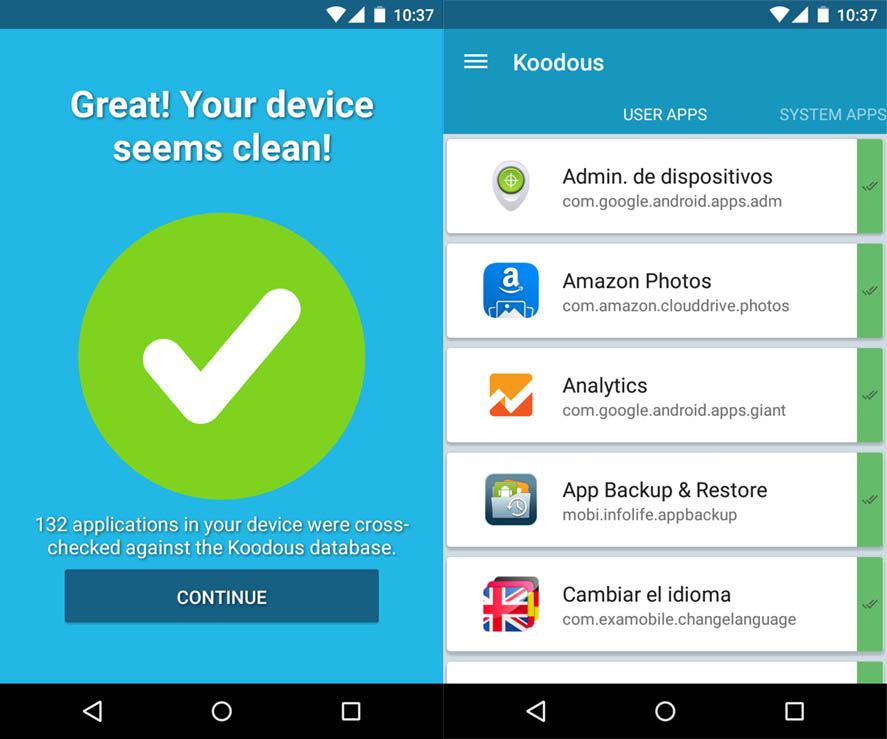
The Android app
Once started, it will do an instant analysis of all your installed apps, including both external and system services. When you finish you’ll get a report that identifies those of questionable provenance. If you hold down on the square for a particular app you can view a small report with (among other info) the requested permissions. Likewise, if you do a quick tap on an app in the list it will ask you if you want to uninstall it.
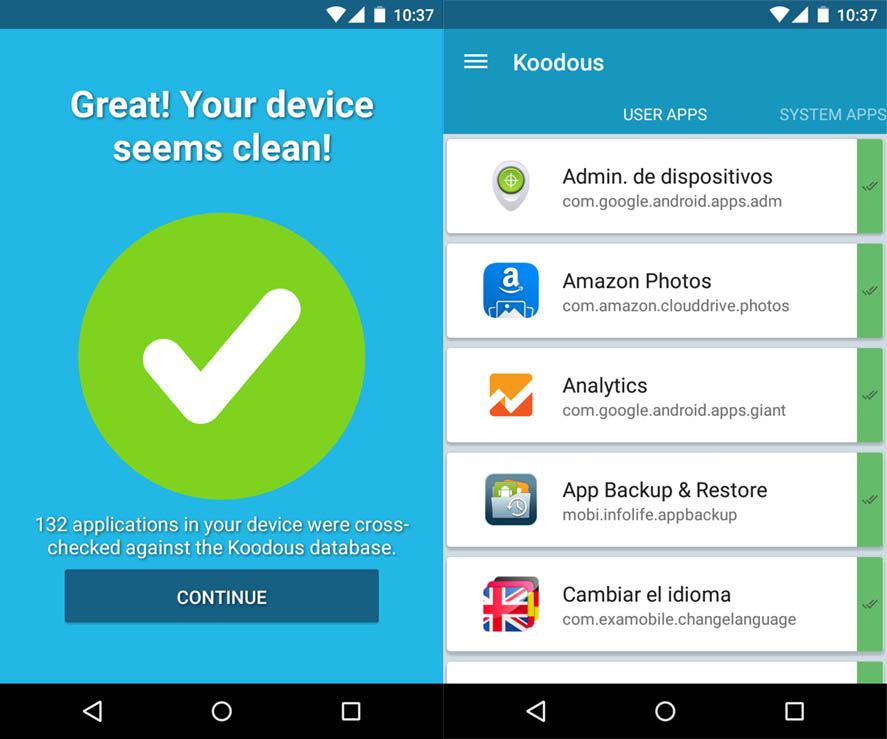
The web service
If you go to the official webpage and enter your details to register you can go to a panel to manage your applications and see feedback from the Koodous community. It currently has close to five million analyzed and catalogued apps, and as noted on the Hispasec blog, out of all of them some million have been classed as malicious. The fact that more than 20% of those analyzed are malicious says a lot about how careful you have to be when you download things from unreliable sources. Best use Uptodown, mate!
The tool’s potential lies in the fact that the reports are made based on the analyses generated in the official app, meaning the database is being constantly reupdated to offer a complete repository from which you can download the scanned apps to contribute to their analysis. Another curious tidbit: if you search for WhatsApp among those five million, you’ll get 7,000 results. If you get rid of the unofficial apps, those with derivative names, and the repeats that come from different sources, you’re still left with hundreds of fake WhatsApp apps. Seriously: BE CAREFUL.
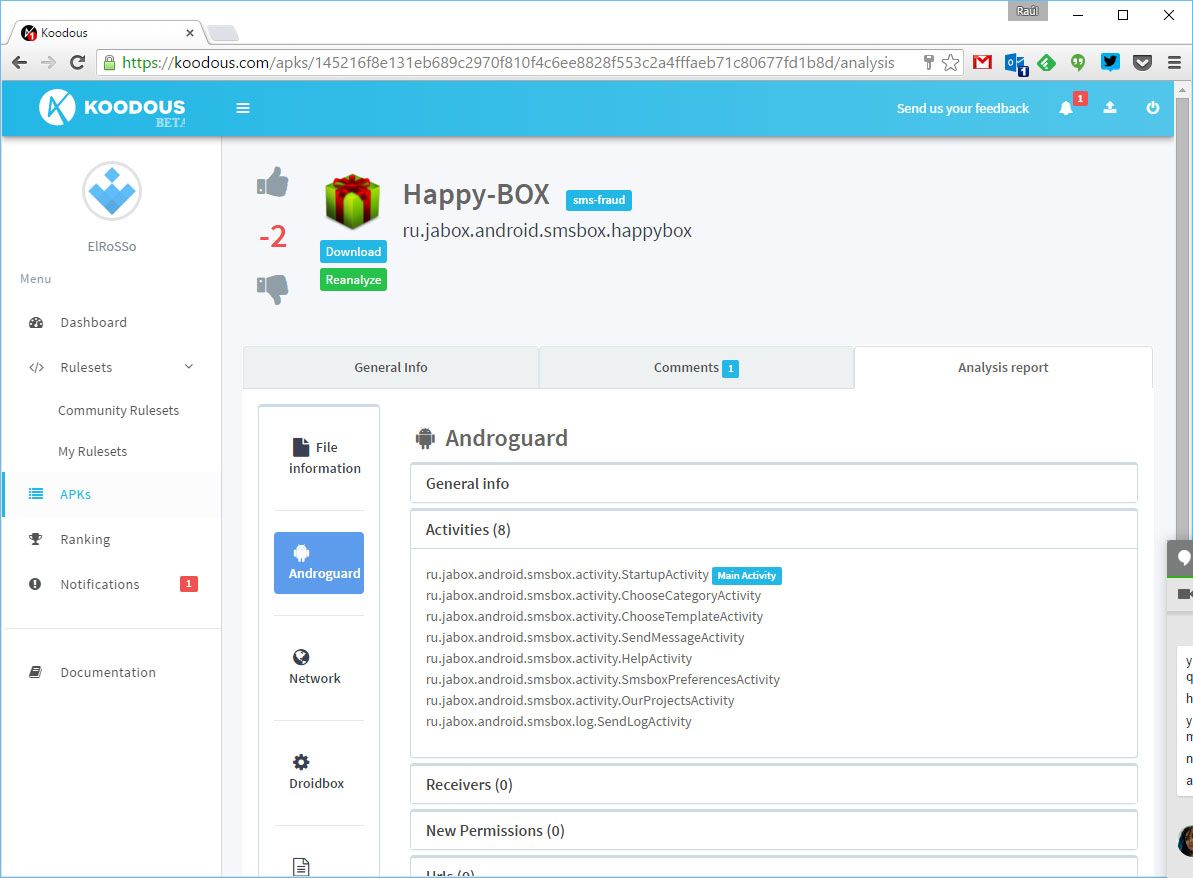
From the service you can upload your own APK file to be analyzed, and also rate other apps, either with comments or by turning to technical procedures such as the app for the so-called YARA rules, which are simply lines of code that analyze an app’s behavior to detect the common modes of functioning to catalogue the malware in question.